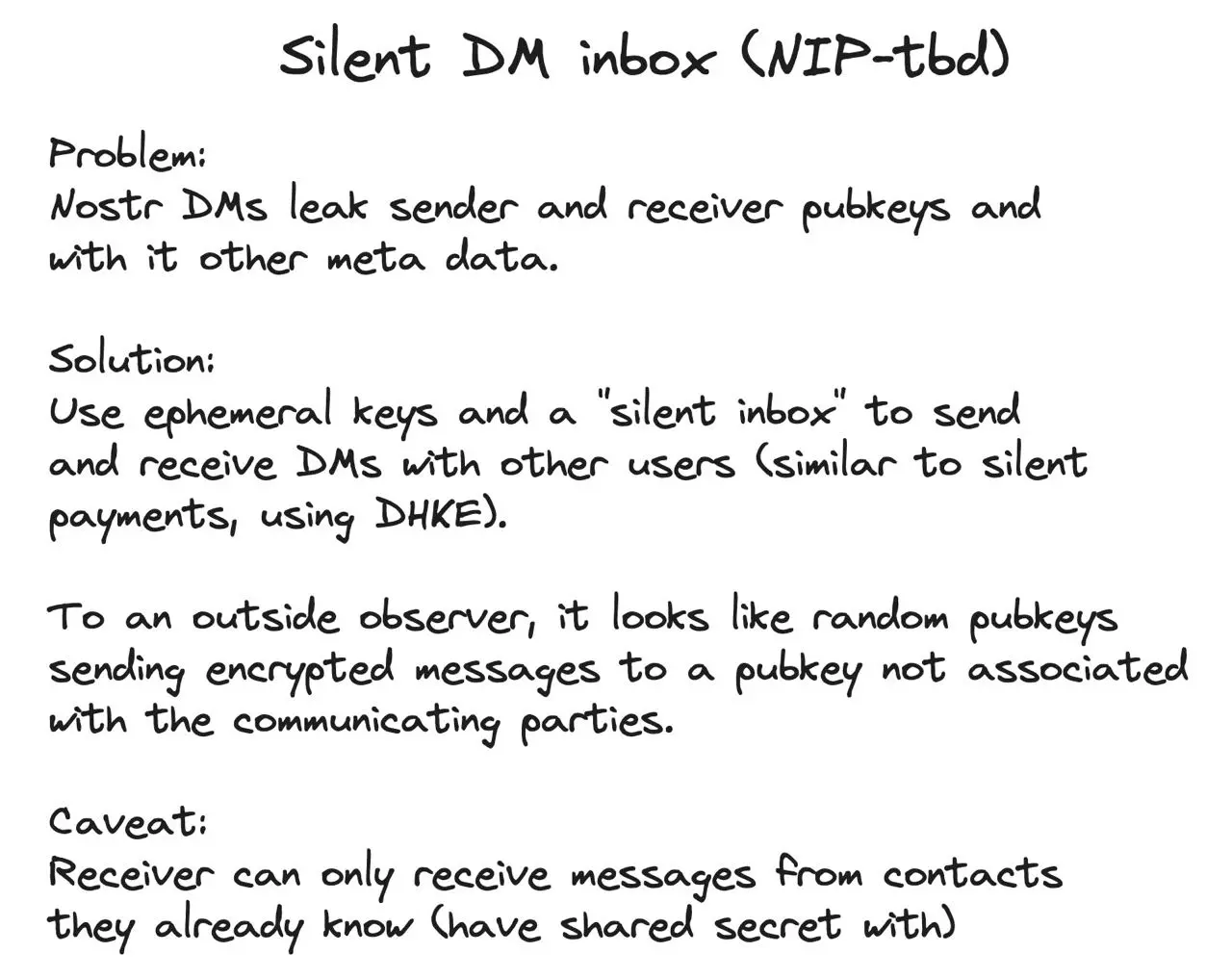
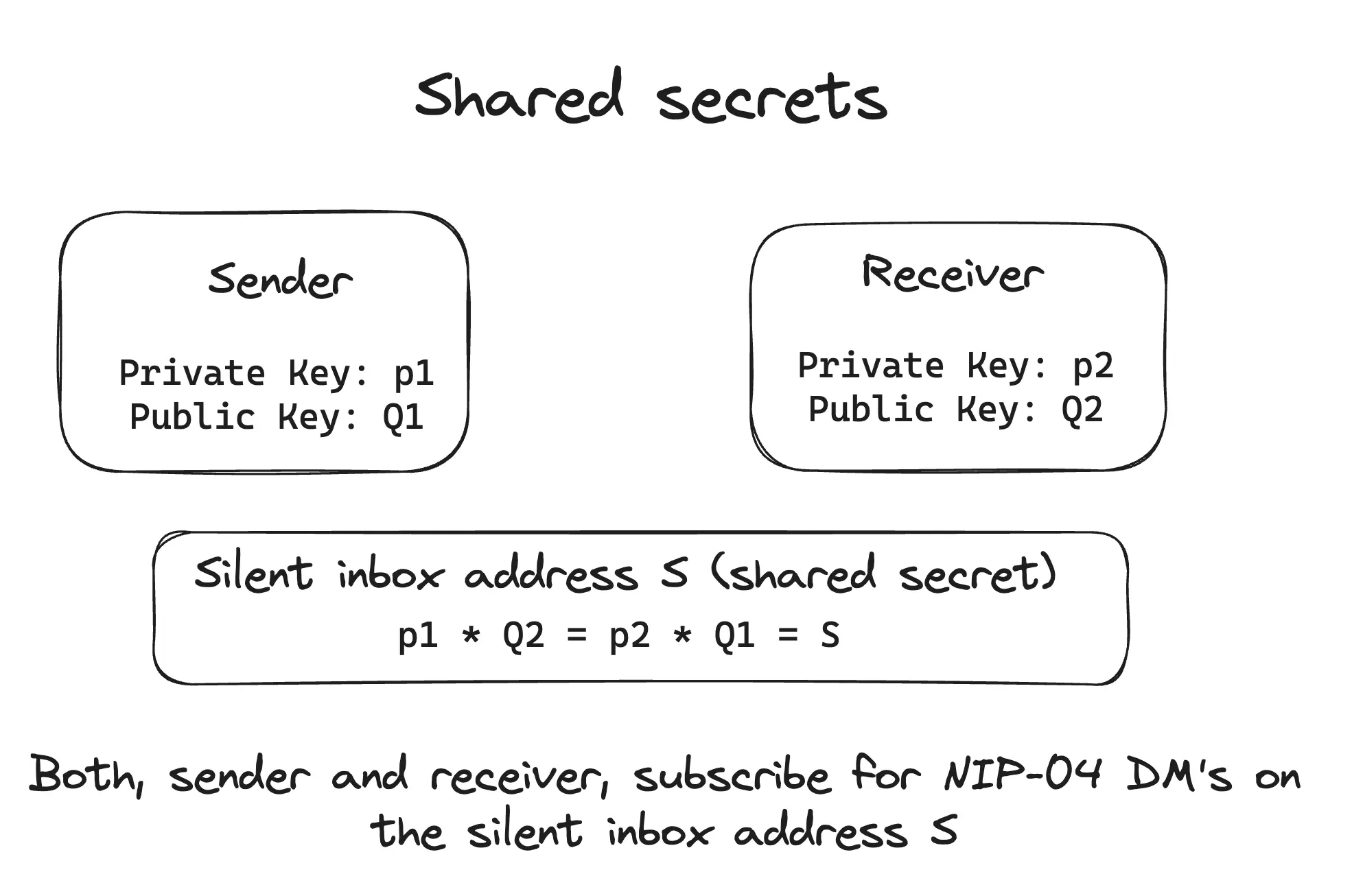
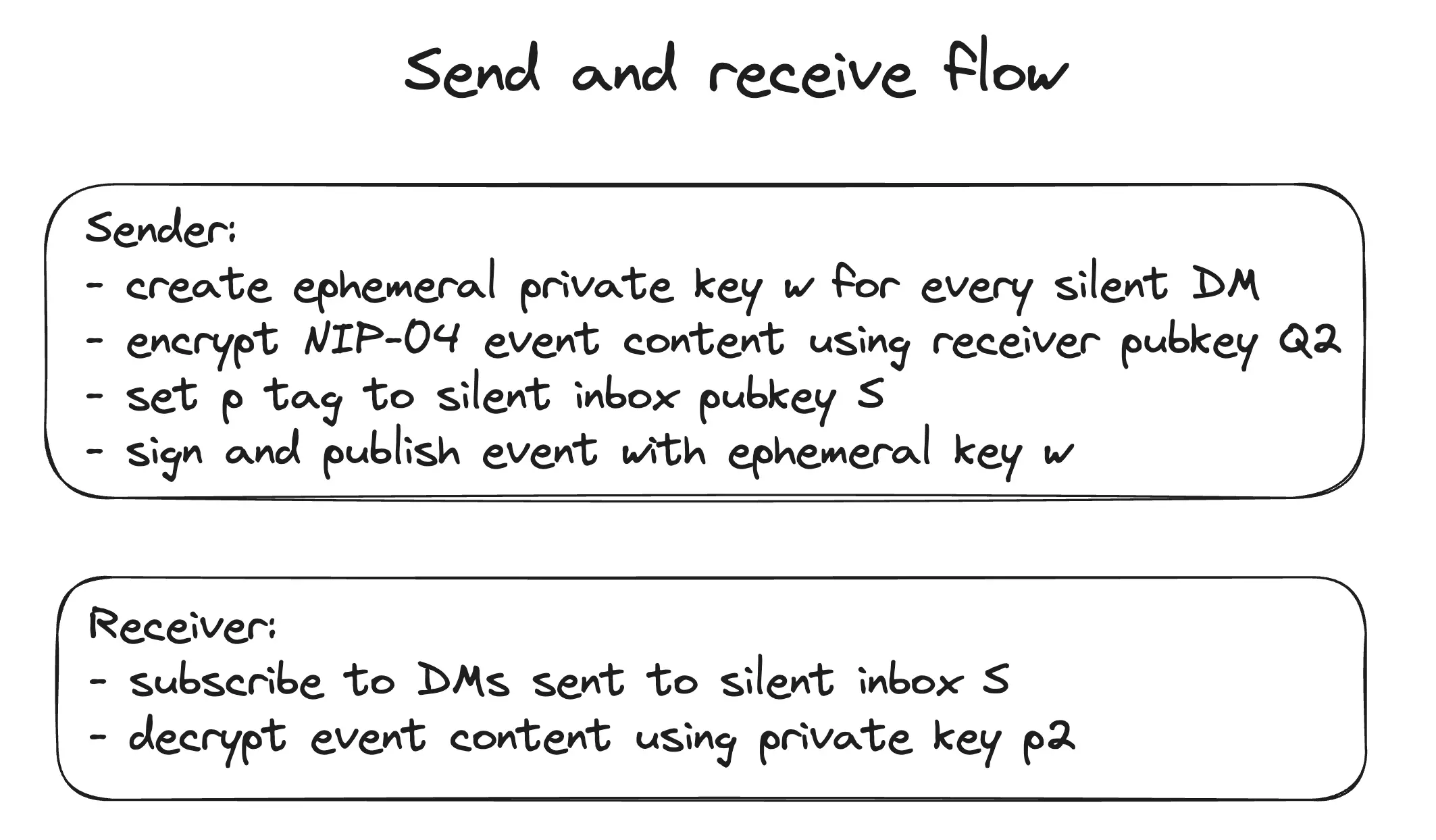
Pretty basic construction of Nostr silent DM's that break the DM graph privacy nightmare.
Others probably have suggested the same thing because it's too damn simple and obvious of a solution. Still gonna put it up here, maybe someone has comments. Might become a NIP proposal if there is interest.
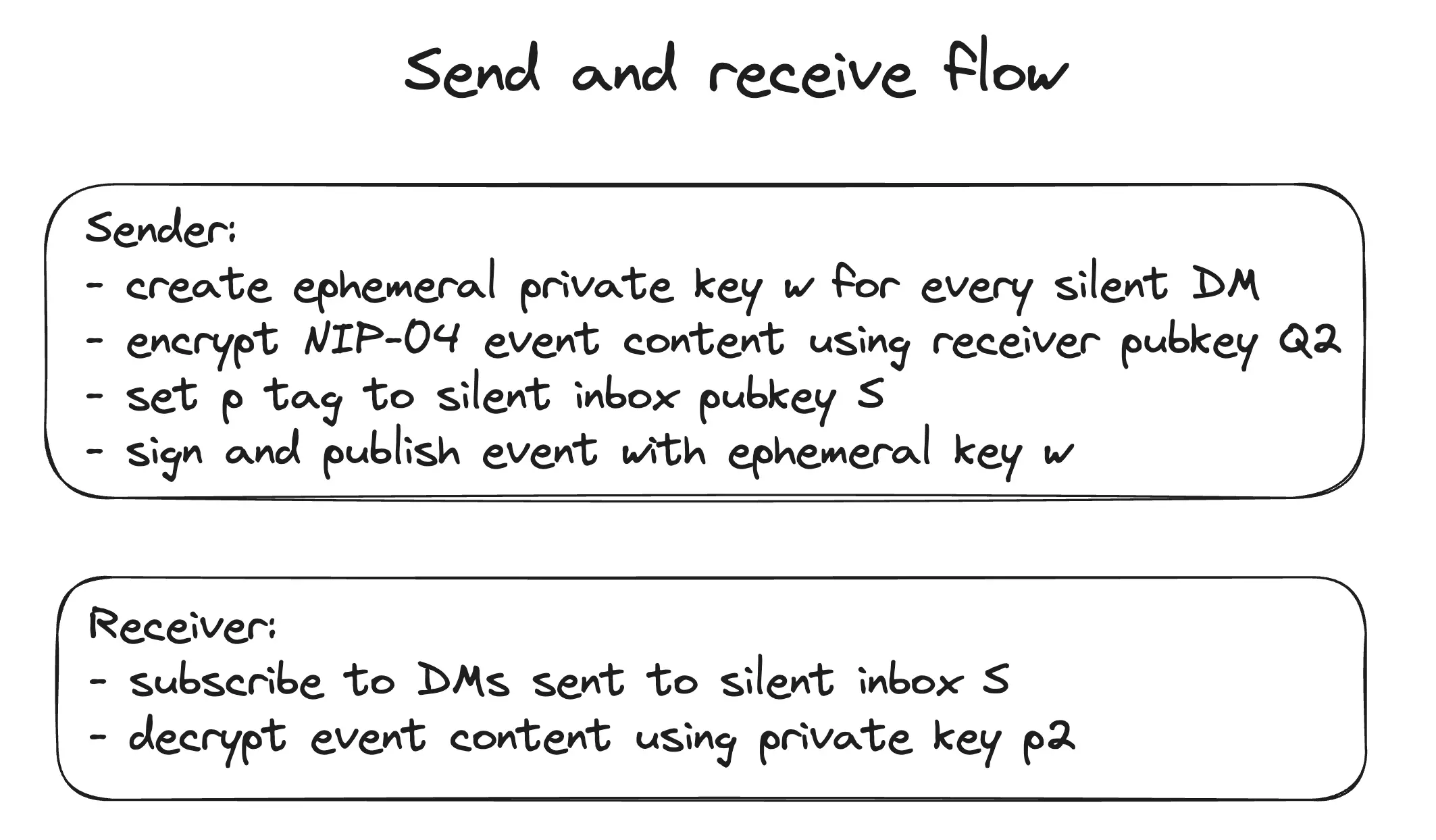
I've coded it up and it works quite nicely.